Microsoft 365
The Microsoft 365 connector provides shared authentication and identity crawling for SharePoint and OneDrive. Set up Microsoft 365 first, then configure SharePoint and OneDrive as child connectors that inherit the parent credentials.
This merged setup flow currently applies to SharePoint and OneDrive only. Outlook and Teams are not part of this setup and continue to be configured separately.
How it works
You register one parent app in Microsoft Entra ID. This app handles identity crawling for your Microsoft 365 tenant and provides credentials that SharePoint and OneDrive inherit automatically.
After saving the Microsoft 365 suite, configure SharePoint and/or OneDrive as child connectors. Each child connector inherits the parent credentials and only requires child-specific configuration.
Required permissions for setup
The user setting up this data source must be the Global Admin.
Register a new app
- Sign in to the Azure portal.
- Select Microsoft Entra ID → Manage → App registrations → New registration.
- On the Register an application page, register an app with the following:
| Field | Value |
|---|---|
| Name | Glean |
| Supported account types | Accounts in this organizational directory only (Single tenant) |
| Redirect URI | Leave this field blank |
- Click Register.
Configure permissions
-
On the overview page, click Manage → API Permissions.
-
Click Add a permission and select Microsoft Graph.
-
Choose Application permissions and add the following:
User.Read.AllGroupMember.Read.AllReports.Read.AllMember.Read.Hidden
SharePoint and OneDrive may require additional content permissions on this same app. Add those permissions during child connector setup.
Grant admin consent
- Ensure you are signed in to Azure as a Global, Application, or Cloud Application Administrator.
- Use the search box to navigate to Enterprise applications.
- Select the Glean app you created.
- Click Permissions under Security.
- Review the permissions shown, then click Grant admin consent.
Set up certificate authentication
Install OpenSSL
OpenSSL is installed by default on macOS terminals. If you are using Windows, follow these instructions to download OpenSSL for use with PowerShell.
- Download the relevant OpenSSL installation manager for your version of Windows. OpenSSL offers a list of third-party binary distributions, with Shining Light Productions as an option.
- During the installation process, select the option to copy the OpenSSL binaries into the
/bindirectory. - Open a new PowerShell instance and run the following command to make OpenSSL binaries available:
$env:Path += ";C:\\Program Files\\OpenSSL-Win64\\bin"
Generate certificate and private key
Run the following commands line by line. Microsoft SDK requires the certificate to be verified with a private key in PKCS#8 syntax.
openssl genrsa -out tempprivatekey.key 2048
openssl pkcs8 -topk8 -inform PEM -outform PEM -in tempprivatekey.key -out privatekey.key -nocrypt
openssl req -new -key privatekey.key -out request.csr
openssl x509 -req -days 365 -in request.csr -signkey privatekey.key -out certificate.crt
Verify that both certificate.crt and privatekey.key exist. Open each file and confirm the formats:
- The certificate file should start with
BEGIN CERTIFICATEand end withEND CERTIFICATE. - The private key should begin with
BEGIN PRIVATE KEYand end withEND PRIVATE KEY. It should not includeRSAin the headers, nor be encrypted.
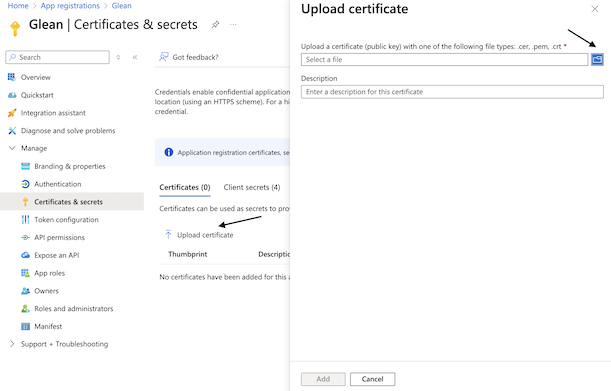
Upload certificate to Azure
- Navigate back to Microsoft Entra ID → Manage → App registrations and select the app you created.
- Click Manage → Certificates & secrets.
- Click the Certificates tab and then Upload certificate.
- Upload the
certificate.crtfile you generated.
Fill out keys
-
In Azure, click Overview.
-
Copy the following values from the Essentials panel and enter them in Glean:
- Application (client) ID
- Directory (tenant) ID
-
Upload
certificate.crtin Glean under Client Certificate. -
Upload
privatekey.keyin Glean under Private Key. -
Select your tenant size in Glean.
-
Click Save to create the Microsoft 365 suite.
If your tenant size is greater than 1000, add 5 additional applications to improve full crawl speed. In general, Glean recommends between 1 and 10 additional applications with the same permission settings as the initial app created.
For each additional app, repeat the steps from Register a new app through Upload certificate to Azure, then paste the additional Application (client) ID into Glean. You only need to upload the certificate once in Glean.
After saving the Microsoft 365 suite, continue setting up SharePoint and OneDrive. Those child connectors inherit the parent credentials. If a SharePoint or OneDrive child connector later needs additional permissions for content crawling, add them to this same app and any additional apps during child setup.