Microsoft Dynamics 365
The Glean Microsoft Dynamics 365 connector indexes data from Dynamics 365.
After you set up the connector and a crawl completes, users can search for this CRM context in:
- Glean Search
- Glean
- Glean Agents
- Glean MCP
Supported tables
By default, Glean indexes the following Dynamics 365 tables:
- Accounts
- Contacts
- Leads
- Opportunities
- Activities, including emails, meetings, and attachments
Glean can also index additional Dynamics 365 tables. To include additional tables in the index, contact Glean Support.
Supported features
- Index all Dynamics 365 tables, including Microsoft-provided and customer-defined tables.
- Index columns from all selected tables.
- Perform full and incremental crawls to keep data current.
- Discover table schemas and column metadata automatically.
- Glean mirrors Dynamics 365 role-based access using security roles and read scopes. Role-based read access can apply at the organization, business unit, or parent:child business unit level. For more information, see Microsoft’s Security roles and privileges for Dataverse.
- Glean mirrors Dynamics 365 hierarchy-based access when hierarchy security is enabled for the connector deployment and in the Dynamics 365 organization.
- Supported hierarchy modes are manager hierarchy and position hierarchy. In Dynamics 365, manager hierarchy follows the reporting chain, while position hierarchy follows the configured position structure rather than direct reporting lines. For details, see Microsoft’s Hierarchy security documentation.
- Customize indexing by greenlisting tables or redlisting columns. Contact Glean Support to greenlist customer-defined tables for indexing or redlist columns for exclusion. These settings are not available in the Glean setup UI.
Supported API endpoints
- Dynamics CRM API (delegated permission:
user_impersonation)
When hierarchy security is enabled, Glean also reads Dynamics 365 hierarchy settings, hierarchy exclusions, and position hierarchy data to mirror access correctly.
Limitations
- Sharing-based ACLs are not supported.
- You can connect only one Dynamics 365 organization (tenant) per Glean data source instance (DSI).
Crawling strategy
| Crawl type | Full crawl | Incremental crawl | People data | Activity | Update rate | Webhook | Notes |
|---|---|---|---|---|---|---|---|
| Dynamics 365 CRM | Yes | Yes | No | No | Timely | N/A | Indexes default tables by default and can index additional tables when configured by Glean Support; one org per DSI |
Requirements
The following requirements must be met to use the Dynamics 365 connector.
Technical requirements
- Microsoft Dynamics 365 environment must be licensed and accessible within your organization.
- An O365 data source (OneDrive or SharePoint) set up in Glean and linked to the same Azure tenant as Dynamics 365.
- Azure portal access for registering and managing applications.
- To use hierarchy-based access, hierarchy security must already be enabled in your Dynamics 365 environment, and Glean must enable hierarchy security for the connector deployment. For setup details, see Microsoft’s Hierarchy security documentation.
Credential requirements
- You must generate and provide:
- Application (client) ID
- Directory (tenant) ID
- Client secret
- Dynamics 365 organization ID
These credentials are configured and obtained during the Azure portal setup. Only admin-level users (Global administrator, Application administrator, or Cloud Application administrator) must complete this process.
Permission requirements
- Microsoft 365 and Azure admin privileges are required for setup and granting consent.
- The new Azure application must have:
- Dynamics CRM (delegated): user_impersonation
- You must assign a Dynamics 365 security role to the application user (recommended: System Administrator, or a custom org-level read-only role with appropriate table access).
- Admin consent must be granted on the app in Azure Enterprise Applications.
Configuration and setup instructions
Required permissions for setup
- The user setting up this data source must be the Global Admin.
1. O365 data source association
- Ensure some O365 data source (for example, OneDrive or SharePoint) with Dynamics 365's Azure tenant ID is already set up.
2. Register a new app
-
Sign into the Azure portal. Select Microsoft Entra ID, then Manage → App registrations → New registration.
-
On the Register an application page, register an app with the following:
Field Value Name GleanSupported account types Accounts in this organizational directory only (Single tenant) Redirect URI (Leave this field blank) -
Click Register.
3. Configure permissions
-
On the left side navigation on the overview page, click on Manage → API Permissions.
-
Click Add a permission and select Dynamics CRM. Select Delegated permissions and add the following:
user_impersonation
4. Grant admin consent
-
Ensure you are signed into Azure as a Global administrator, Application administrator, or Cloud Application administrator.
-
Use the search box to navigate to Enterprise applications. Select the Glean app you created from the list of applications.
-
Click Permissions under Security. Review the permissions shown, and then click Grant admin consent.
By this step, you must have the Dynamics CRM user_impersonation permission provisioned on the API Permissions page.
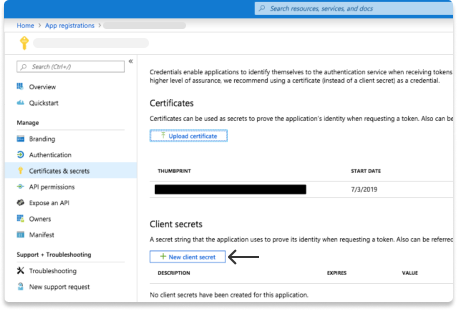
5. Generate secret
-
Navigate to Microsoft Entra ID → Manage → App registrations and click on the app you created earlier.
-
Click Manage → Certificates & secrets in the left sidebar.
-
Click on New client secret. Enter a description and select 24 months for expiry time, then click Add.
-
Under Client secrets, copy the Value (not the Secret ID) you generated and enter it in Glean as the Client secret. The Value is shown only once.
6. Get Dynamics 365 organization ID
- Check the URL bar in your browser. The Dynamics 365 Organization ID is part of the domain name. For example if you see:
https://org810c0cef.crm.dynamics.com/in the URL bar, your Organization ID isorg810c0cef.
7. Add application user in Dynamics 365
-
Sign into the Power platform admin center.
-
Select the Dynamics 365 environment you want to connect to Glean.
-
On the Dynamics 365 environment page, navigate to Settings → User + permissions → Application users to add a new application user.
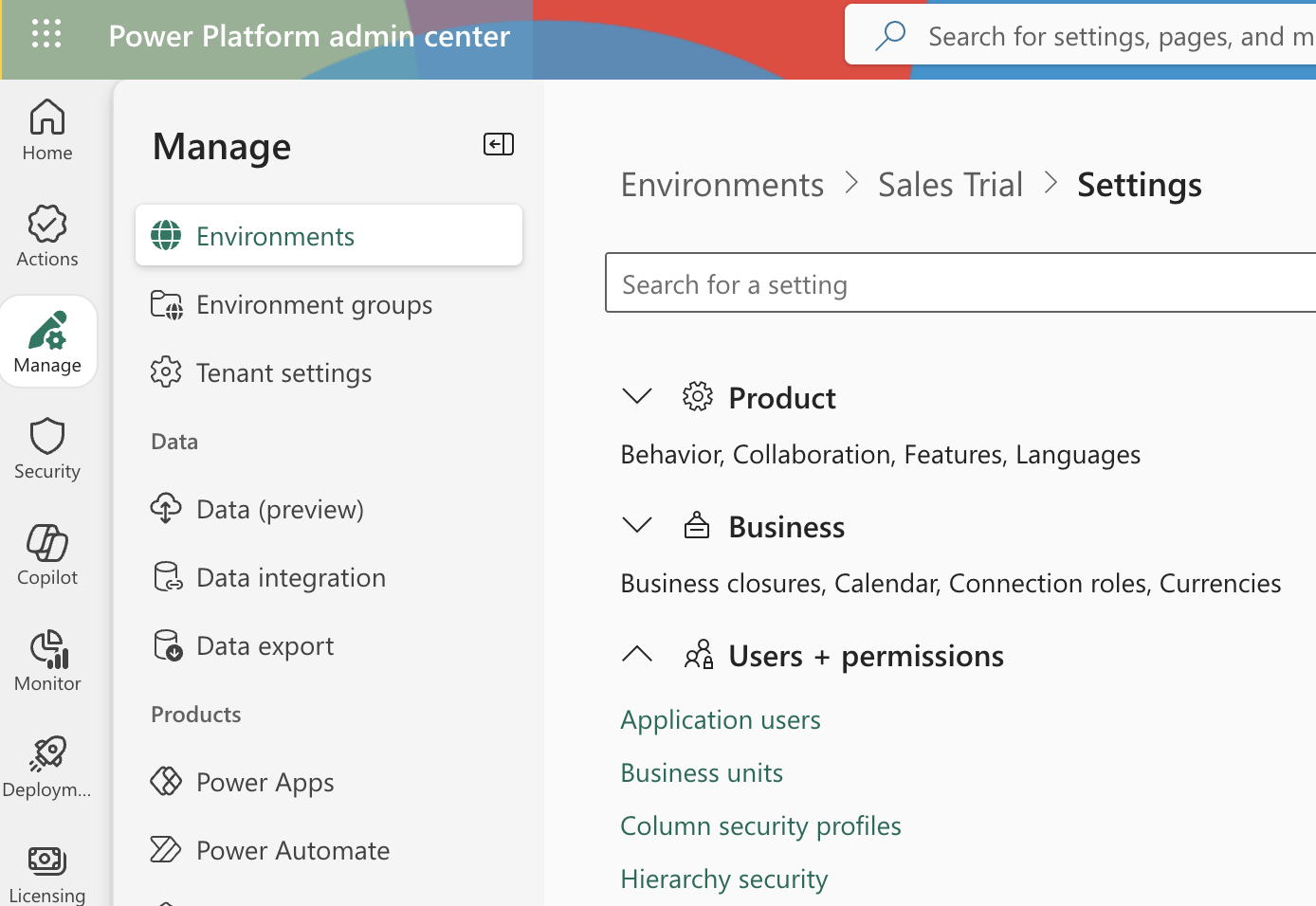
-
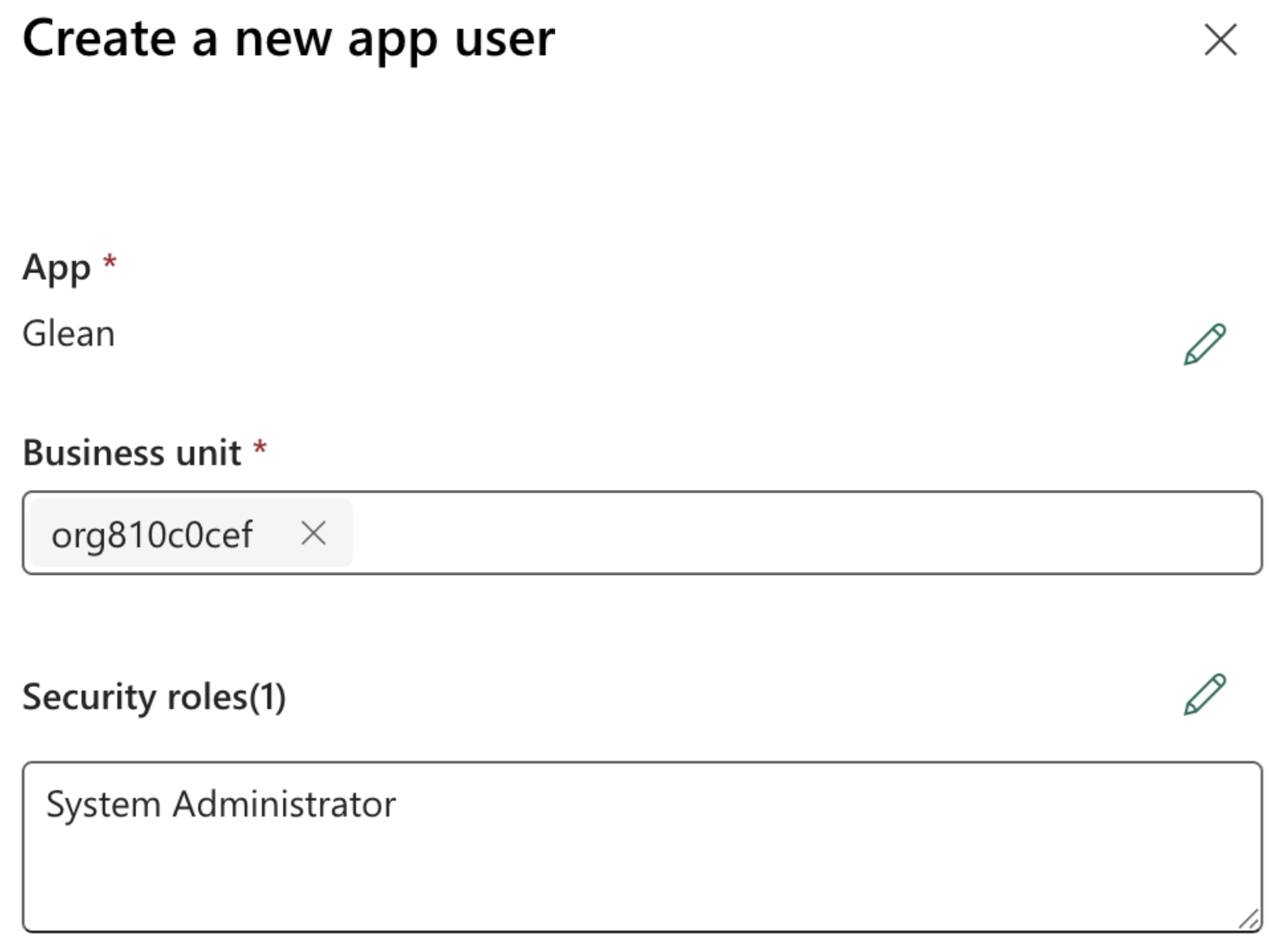
On the Application users page, click + New app user to open the Create a new app user dialog.
-
Enter the previously created app name, Dynamics 365 organization ID, and role name that provides read access to the Dynamics 365 data, then click Create.
8. Fill out keys
- Scroll to the top of the left sidebar and click Setup.
- Copy the Application (client) ID and Directory (tenant) ID and enter them in the Glean self-serve page.
- Enter the Dynamics 365 Organization ID in the designated field.
- Click Save. If the credentials save, you're all set!
Permissions and security
Data and metadata ingested
- Data: Accounts, Contacts, Opportunities, Leads, Activities (email, meetings, attachments), additional greenlisted tables, indexed columns, and metadata (timestamps, owners, and so on)
- Identity mappings support access control mirroring Dynamics 365 security roles and business units. When hierarchy security is enabled, Glean also uses Dynamics 365 hierarchy settings and exclusions to expand access appropriately.
Permission propagation logic
- Glean respects Dynamics 365 record access, so users can only see records they can access in the source system.
- Role-based access is the base permission model.
- When hierarchy security is enabled, Glean also mirrors hierarchy-based access from Dynamics 365.
- Glean respects the maximum hierarchy depth configured in Dynamics 365.
- If a table is excluded from hierarchy security in Dynamics 365, Glean does not apply hierarchy-based access expansion for that table.
- Additional indexed tables follow the same permission model as the default indexed tables.
How hierarchy-based access works
Glean supports Dynamics 365 hierarchy security to ensure that access in Glean matches your organizational structure.
- Manager hierarchy: Users inherit access to records owned by or shared with their direct and indirect reports.
- Position hierarchy: Users inherit access based on their relative level in the configured position hierarchy.
- Activation: Hierarchy-based access applies only when hierarchy security is enabled in both Dynamics 365 and the Glean connector settings.
- Update cadence: Hierarchy-related permission changes are not applied in real time. Updates take effect after the next hierarchy crawl and subsequent content reprocessing.
How role-based access works
Glean uses Dynamics 365 security roles to determine record-level access based on the following logic:
- Security roles: Glean respects the read access level configured in Dynamics 365, whether permissions are granted at the Organization, Business Unit, or Parent:Child Business Unit level.
- Owner-based access: Glean also respects owner-based read access for records owned by a user or team.
- Permissions mapping: Glean maps Dynamics 365 read privileges for indexed tables to record access in Glean so search results stay aligned with Dataverse security. For details, see Microsoft’s Security roles and privileges for Dataverse.
Security and compliance notes
- Authentication uses OAuth2 against Azure AD.
- Glean does not modify or create data in your Dynamics 365 environment.
- Supported for one Dynamics 365 organization per Glean data source instance.
Data privacy implications
- Indexed CRM data may include personally identifiable information (PII) as present in source records.
- Role-based access protects sensitive records from unauthorized views in Glean.
- No external data sharing or writing occurs during crawl.

