SharePoint setup (Native)
Required permissions for setup
- The user setting up this data source must be the Global Admin.
Register a new app
- Sign into the Azure portal.
- Select Microsoft Entra ID → Manage → App registrations → New registration.
- On the Register an application page, register an app with the following:
| Field | Value |
|---|---|
| Name | Glean |
| Supported account types | Accounts in this organizational directory only (Single tenant) |
| Redirect URI | (Leave this field blank) |
- Click Register.

Configure permissions
-
On the overview page, click on Manage → API Permissions.
-
Click Add a permission.
-
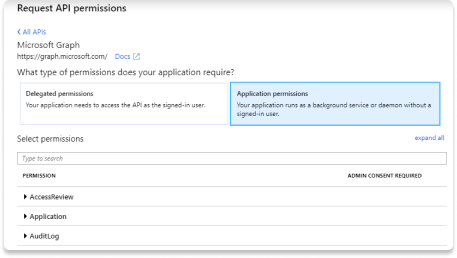
Select Microsoft Graph.
-
Choose Application permissions and add the following:
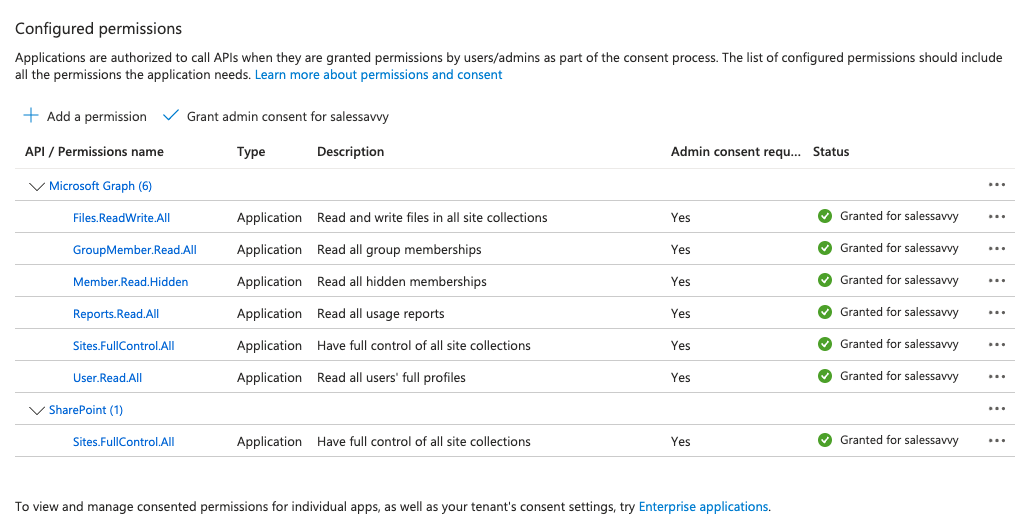
User.Read.AllGroupMember.Read.AllFiles.ReadWrite.All(for subscriptions over drives)Reports.Read.AllSites.FullControl.AllMember.Read.Hidden
- Click Add a permission and select Sharepoint.
- Choose Application permissions and add the following:
Sites.FullControl.All
Grant admin consent
-
Ensure you are signed into Azure as a Global, Application or Cloud Application administrator.
-
Use the search box to navigate to Enterprise applications.
-
Select the Glean app you created from the list of applications.
-
Click on Permissions under Security. Review the permissions shown, and click Grant admin consent.

You must have the following permissions provisioned on the API Permissions page:
Install openssl
Openssl is installed by default on OS X terminals. If you are using Windows, follow these instructions to download openssl to use with PowerShell.
-
Download the relevant openssl installation manager for your version of Windows. Openssl offers a list of third-party binary distributions, with Shining Light Productions as an option.
-
During the installation process, select the option to copy the OpenSSL binaries into the
/bindirectory. -
Open a new PowerShell instance. In PowerShell, you can run the following command to make use of openssl binaries.
$env:Path += ";C:\\Program Files\\OpenSSL-Win64\\bin"
Generate Certificate and Private Key
- Run the following commands line by line. Microsoft SDK requires the certificate to be verified with a private key in PKCS#8 syntax.
openssl genrsa -out tempprivatekey.key 2048
openssl pkcs8 -topk8 -inform PEM -outform PEM -in tempprivatekey.key -out privatekey.key -nocrypt
openssl req -new -key privatekey.key -out request.csr
openssl x509 -req -days 365 -in request.csr -signkey privatekey.key -out certificate.crt
- Verify that both `certificate.crt` and `privatekey.key` exist. Open each file, and ensure the files conform to the following formats:
- The certificate file must start with
-----BEGIN CERTIFICATE-----and end with-----END CERTIFICATE----- - The private key should begin with
-----BEGIN PRIVATE KEY-----and end with-----END PRIVATE KEY-----. It must not includeRSAin the headers, nor be encrypted.
-
Upload the `certificate.crt` in Glean under Client Certificate.
-
Upload the `privatekey.key` in Glean under Private Key.
Upload Certificate to Azure
-
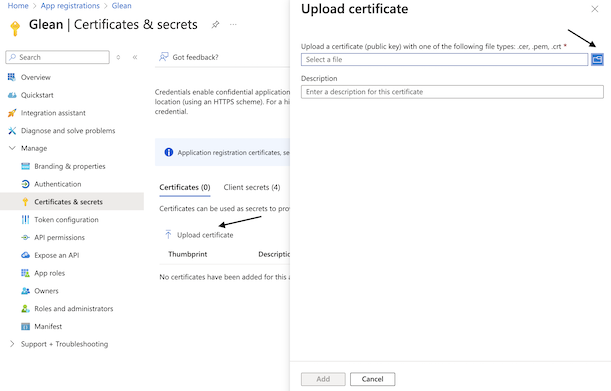
Navigate back to Microsoft Entra ID → Manage → App registrations and click on the app you created earlier.
-
Click Manage → Certificates & secrets.
-
Click the Certificates Section and Upload certificate.
-
Upload the `certificate.crt` file that you generated. After uploading, the application must now list the new certificate.
Fill out keys
-
Scroll to the top of the left sidebar and click Overview.
-
Copy the following content from the center Essentials panel and enter it in Glean:
- Application (client) ID
- Directory (tenant) ID
-
Enter your Sharepoint domain in Glean. Your Sharepoint domain must end with sharepoint.com.
-
Glean recommends to increase the full crawl indexing speeds. It is recommended to have between 1 and 10 additional applications with the same permission settings as the initial app created.
-
Repeat the setup steps from Register a new app until this step, saving the client ID and uploading the certificate to Azure in the process. Paste the client ID into the Glean web app.

- Click Save.